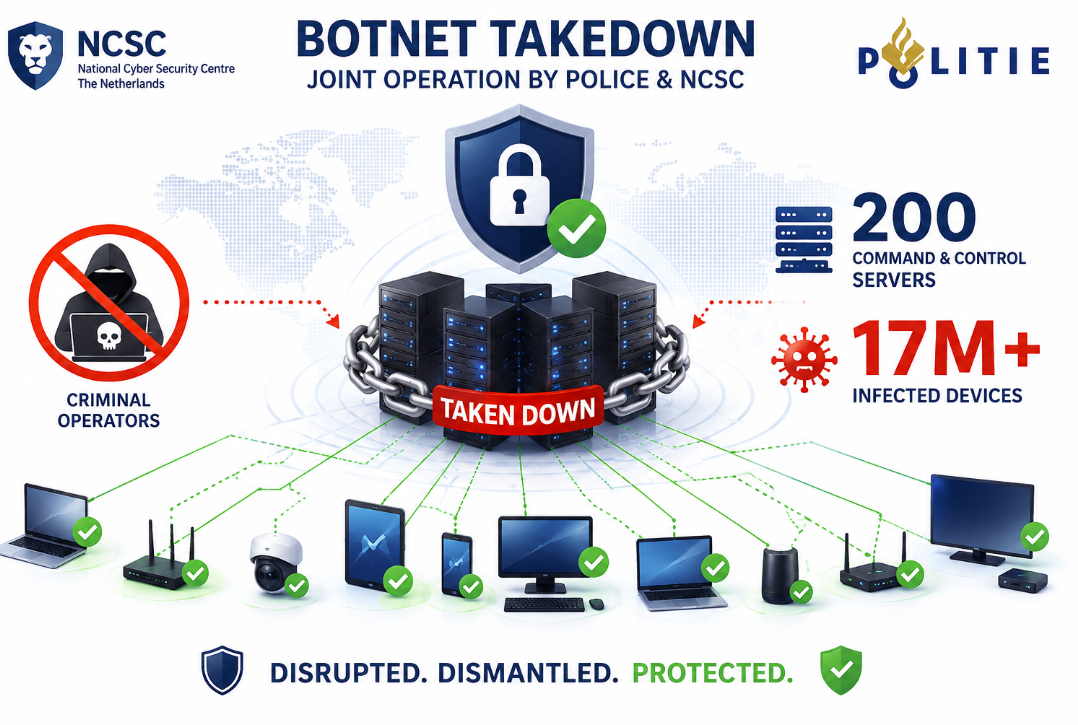
17 Million Infected Devices: Why the Dutch Botnet 17 Million Infected Devices: Why the Dutch Botnet Takedown Is a Wake-Up Call for Every CISO
A joint operation by the Dutch NCSC and Police dismantled a botnet infrastructure controlling at least 17 million infected devices…